From Advanced Intelligence
to Fortified Defense.
Stop chasing signals through noise. ATI turns 14B+ daily attack records into accurate, actionable intelligence with deep APAC coverage and curated detection rules your SOC can use immediately.
























Volume. Accuracy. Actionability. Most threat intelligence platforms can't deliver all three.
Between raw threat data and SOC-ready intelligence, most platforms break down. Analysts close the gap manually.
Data Overload, Wasted Analysis
Analysts sift through indicators from dozens of open-source and vendor feeds, but the signal-to-noise ratio is low. Hours go to filtering rather than hunting. Threat hunting becomes data janitoring.
Inaccurate IOCs, Endless False Positives
Low-quality indicators flood SIEMs with false positives. Without accuracy context and enrichment, analysts burn hours chasing alerts that lead nowhere. Real threats slip past during the noise.
High-Level Reports, No Defensive Guidance
Most intelligence reporting describes threat actors in strategic terms: broad campaign narratives without the TTPs, malware behaviors, or ready-to-use detection rules that detection engineers actually need.
Broken Integration, Siloed Teams
Pushing validated intelligence into SIEMs, SOARs, and firewalls is still a largely manual process. The disconnect between TI teams and SOC teams creates friction that slows response and allows threats to persist.
A Threat Intelligence Portal that turns raw attack data into SOC-ready decisions.
ThreatBook ATI aggregates 14B+ daily attack records across honeypots, OSINT, DFIR cases, and 23 years of WHOIS data, then distills it into accurate, machine-readable intelligence with an AI engine that connects the dots across actors, malware, and infrastructure. The result is intelligence your SOC can act on the same day it arrives.
- 99.9% IOC accuracy rate — fewer false positives, faster triage
- Deep APAC perspective with global coverage — the threats targeting your region, in detail
- Ready-to-deploy detection rules — YARA, Sigma, Suricata, and Zeek, mapped to MITRE ATT&CK
- API and STIX feeds for direct SIEM, SOAR, and TIP integration
Six principles. One outcome: your SOC acts faster.
ATI is engineered around six core capabilities (the 6A framework) that take intelligence from raw collection to decisive action.
Exclusive Proprietary Reports
Elite threat researchers deliver deep-dive intelligence reports on sophisticated campaigns and actors — content you won't find in commercial or open-source feeds.
AI-Powered Investigation Engine
An AI assistant automatically surfaces connections across massive threat datasets, accelerates complex investigations, and generates tailored investigation reports in minutes.
APAC-Focused, Globally Covered
Specialized intelligence on the threat actors, campaigns, and infrastructure targeting the Asia-Pacific region — backed by 14 years of PDNS data and the largest CTI community in Asia.
99.9% Verified Indicators
Machine-readable IOCs validated by a multi-layer verification system. High accuracy means fewer false positives in your SIEM and less analyst fatigue chasing noise.
Detection Rules, Ready to Deploy
Curated detection content in YARA, Sigma, Suricata, and Zeek formats. Structured threat reports with 50+ standard attributions auto-mapped to the MITRE ATT&CK framework.
Faster Intelligence Lifecycle
From data collection to operational response, the entire intelligence lifecycle is accelerated. PIRS monitoring delivers custom real-time alerts on the specific threats that matter to your organization.
From raw data to SOC action in three steps.
ATI connects a world-class data engine to your existing security stack. No rip-and-replace required.
Collect & Enrich
ATI continuously aggregates threat data from honeypots, OSINT (open and dark web), DFIR cases, and 14+ years of passive DNS — processing 14B+ attack behaviors every day and analyzing 2M+ files per day in a cloud sandbox.
Analyze & Verify
The AI engine links indicators to threat actors, malware families, and campaign infrastructure. A multi-layer verification pipeline validates every IOC to 99.9% accuracy and maps findings to MITRE ATT&CK automatically.
Operationalize
Validated intelligence flows into your security stack via API, STIX feeds, or the ATI portal. Detection rules deploy to your SIEM, SOAR, or firewall. Your team acts — not reacts.
Five intelligence entities. One complete picture.
ATI organizes its entire dataset into five structured entity types, so every analyst query returns deep, correlated context, not just a list of indicators.
1,000+ cybercrime groups
80M+ malicious IPs
All with YARA rules
600+ zero-days
Endpoint IOA rules
Every tool your TI team needs. In one portal.
Accessible via web portal, mobile app, REST APIs, and integrated data feeds.
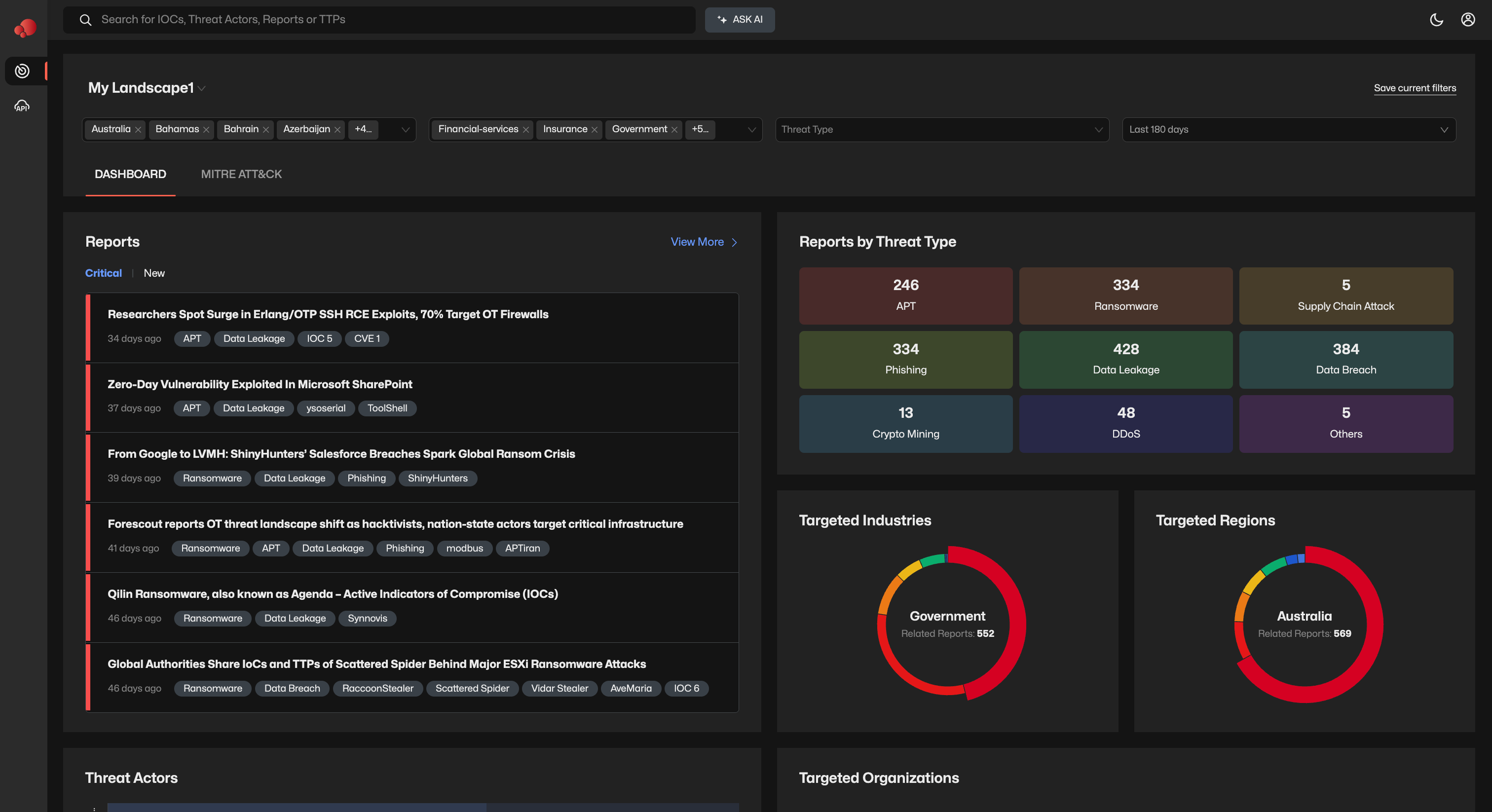
Customizable Threat Landscape
Personalized dashboards and visualizations focused on the actors, vulnerabilities, and TTPs most relevant to your industry and region.
PIRS Monitoring
Define Priority Intelligence Requirements and receive real-time alerts the moment ATI detects activity matching your specific threat topics.
Structured Threat Reports
Reports with 50+ standard attributions, automatically mapped to the MITRE ATT&CK framework — consistent, analyst-ready, and cross-referenceable.
Detailed Threat Actor Profiling
Deep profiles covering motivations, historical campaigns, infrastructure, associated malware, and full TTP breakdowns for 1,200+ tracked actors.
IOC Analysis
Instantly analyze any IP, domain, hash, or URL for a clear malicious verdict, rich context, and attribution links to known actors or campaigns.
Detection Engineering Content
Curated YARA, Sigma, Suricata, and Zeek rules. Network scripts, KQL queries, and malicious code snippets ready for your detection pipeline.
AI-Powered Investigation
An AI assistant uncovers hidden connections across actors, infrastructure, and campaigns — and generates tailored investigation reports automatically.
API & Feeds Integration
High-fidelity REST API and STIX-compliant feeds integrate directly into Splunk, Microsoft Sentinel, Anomali, MISP, and other TIP and SOAR platforms.
Built for how modern SOC teams actually work.
Four high-impact workflows where ATI cuts investigation time and improves response outcomes.
SIEM Alert Triage & Noise Reduction
Challenge: Thousands of alerts daily, no reliable way to prioritize.
By integrating ATI's IP Intelligence API, SIEM alerts are automatically enriched with threat type, actor attribution, and confidence scores. Analysts see immediately whether an IP is malicious — and which actor controls it — so triage takes seconds, not hours.
Automated & Intelligent Response
Challenge: Blocking malicious IPs without disrupting legitimate users.
Before blocking, ATI classifies the IP — mobile gateway, CDN, dynamic range, or confirmed malicious infrastructure. This allows your SOAR to apply granular policies: a 10-minute block for mobile gateways versus a permanent block for C2 infrastructure.
Proactive Compromise Detection
Challenge: Internal hosts communicating with C2 infrastructure can remain undetected for months without DNS telemetry cross-referenced against threat actor data.
Feed DNS logs into ThreatBook's Compromise Detection API. ATI identifies internal hosts communicating with known C2 infrastructure, ransomware command servers, and botnet beacons — providing actor attribution and malware family context for rapid remediation.
Advanced Detection Engineering
Challenge: Maintaining detection coverage against current adversary techniques requires continuous research investment that most security teams cannot dedicate.
ATI provides curated, prioritized detection rules in YARA, Sigma, and Suricata — ranked by real-world exploitation activity, not just CVE severity. Your team deploys detections tuned to threats that are actively targeting organizations like yours.
Works with your existing security stack.
High-fidelity API and STIX-compliant feeds connect ATI to your SIEM, SOAR, and TIP platforms in hours, not weeks. Also available as a premium feed on the Anomali App Store.
Not seeing your platform? Contact us — our team can discuss custom integration options.
Your SOC deserves intelligence that closes the loop.
See how ATI turns 14B+ daily attack records into clear, actionable intelligence — with a personalized demo from our team.