1 min read
How a Malicious Plugin Turned OpenClaw Into a Credential Stealer
Last week, ThreatBook's endpoint detection product, OneSEC EDR, identified and fully captured an active attack targeting OpenClaw users. The attack...
3 min read
![]() ThreatBook Research Team
:
Updated on March 31, 2026
ThreatBook Research Team
:
Updated on March 31, 2026
Axios — one of the most foundational dependencies in the JavaScript ecosystem, with over 3.6 billion annual downloads — was compromised on npm on March 31, 2026. Malicious versions 1.14.1 and 0.30.4 were published using a stolen maintainer account, and automatically download and execute a remote access trojan (RAT) upon installation. The attack affects Windows, Linux, and macOS.
ThreatBook's OneSEC EDR platform detected malicious code executing in real time on machines running OpenClaw. The malicious packages have since been removed by npm, but any environment that installed either affected version should be treated as compromised.


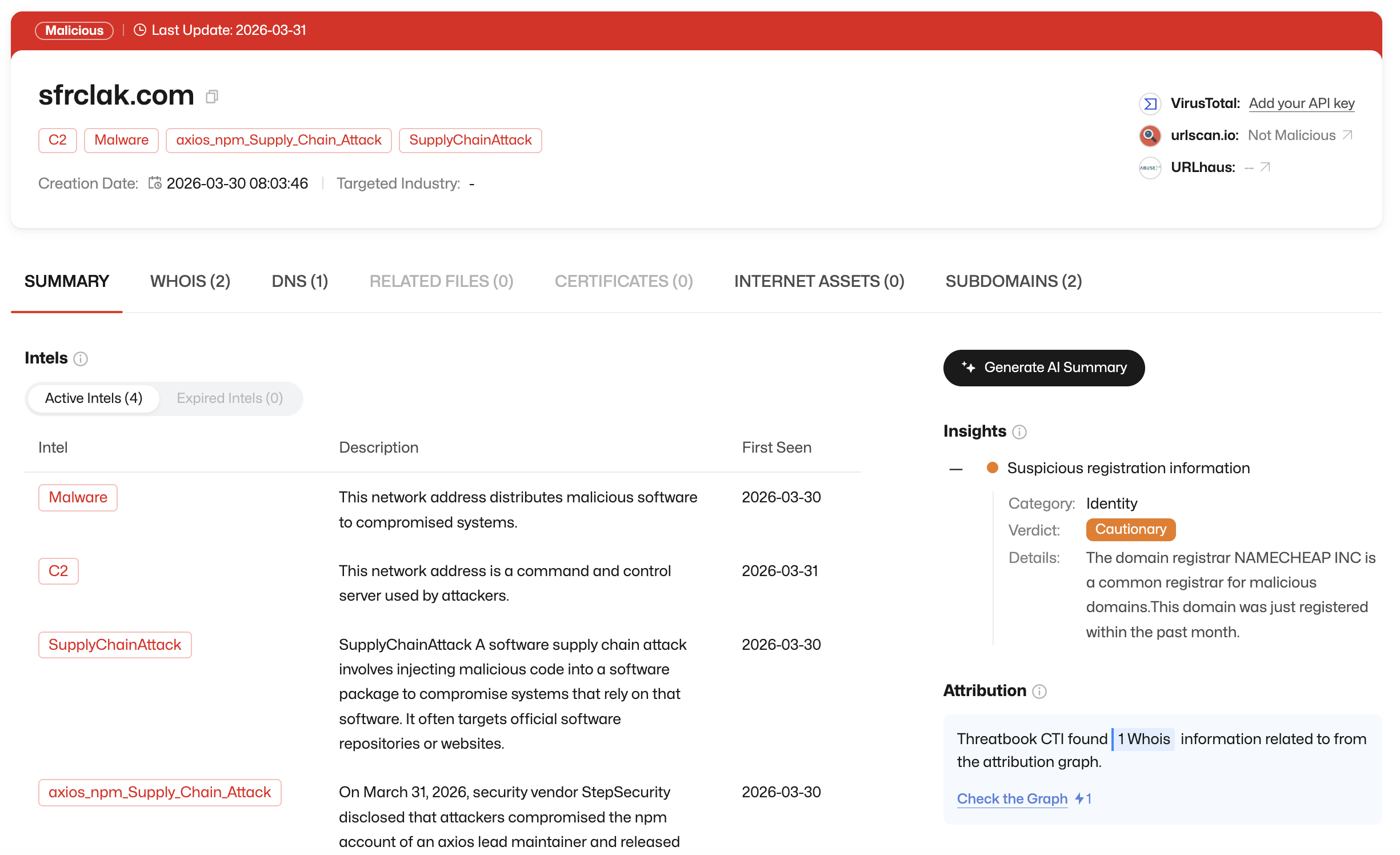
If you see any callback to sfrclak.com in your network logs, your host is compromised. Block this domain immediately and follow the remediation steps below.
| Field | Details |
|---|---|
| Incident | Axios npm supply chain poisoning — cross-platform RAT delivery |
| Affected Package | axios (3.6+ billion annual downloads) |
| Affected Versions | 1.14.1 and 0.30.4 (removed); safe version is 1.14.0 or earlier |
| Discovery | March 31, 2026, ~00:05 UTC (Socket.dev automated detection) |
| Packages Removed | March 31, 2026, ~04:00 UTC |
| Platforms Affected | Windows, Linux, macOS |
| C2 Domain | sfrclak.com |
| Potential Blast Radius | All Node.js and browser applications making HTTP requests — React frontends, CI/CD tooling, server-side APIs |
plain-crypto-js@4.2.1 to npm.axios@1.14.1 and axios@0.30.4, both referencing the malicious dependency.plain-crypto-js as anomalous.plain-crypto-js@4.2.1, axios@1.14.1, and axios@0.30.4 from the registry.On March 30, attackers registered the malicious domain sfrclak.com in preparation for the attack. This domain serves as both the C2 server and payload delivery endpoint.
plain-crypto-js@4.2.1The attack chain flows through a malicious transitive dependency. Both backdoored Axios versions reference plain-crypto-js@4.2.1 in their package.json. This package includes a postinstall hook in its own package.json that triggers execution of setup.js immediately upon installation — before the developer ever runs any application code.
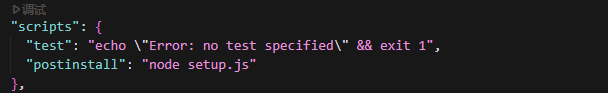
setup.jssetup.js is an obfuscated JavaScript loader. Its function is straightforward: fingerprint the host operating system, then fetch and execute the appropriate platform-specific payload from the attacker's server:
http://sfrclak[.]com:8000/6202033
-png.png?width=1914&height=415&name=download%20(1)-png.png)
This cross-platform targeting — Windows, Linux, and macOS — makes this attack significantly broader in scope than typical supply chain incidents, which often focus on a single OS.
-png.png?width=1456&height=368&name=download%20(2)-png.png)
ThreatBook's Cloud Sandbox S and OneSandbox platforms have confirmed detection of this behavior. The downstream payload is no longer retrievable for analysis, as the delivery URL has been taken down.
ThreatBook's OneSEC EDR detected the malicious code executing during OpenClaw installation on both Windows and macOS endpoints, providing real-time visibility into the attack at the point of execution.
1. Check for network callbacks to sfrclak.com
Any connection to sfrclak.com — inbound or outbound — confirms that the malicious loader executed on that host. Treat the host as compromised and escalate immediately.
2. Block malicious domains at the network layer
sfrclak.comcallnrwise.com3. Audit your Axios version
Check whether your project uses axios@1.14.1 or axios@0.30.4:
bashnpm list axios
-png.png?width=1248&height=129&name=download%20(3)-png.png)
If either affected version is present, remove it and pin to 1.14.0 or an earlier known-good version.
4. Check for plain-crypto-js in node_modules
The presence of the plain-crypto-js directory in node_modules is sufficient to confirm the setup.js loader executed — even if the directory contents appear clean. The stub files may have been replaced after execution.
-png.png?width=1251&height=87&name=download%20(4)-png.png)
-png.png?width=1251&height=417&name=download%20(5)-png.png)
5. Treat CI/CD pipelines as compromised
Any pipeline that ran an install of axios@1.14.1 or axios@0.30.4 should be considered compromised. Rotate all secrets and tokens injected into those pipelines immediately.
6. Check for RAT artifacts on affected systems
Audit running processes and persistence mechanisms on any host where the affected versions were installed. Engage your security team for a full forensic review.
ThreatBook's OneSEC endpoint security platform detected malicious code execution during OpenClaw installation on Windows and macOS hosts in real time.
The following ThreatBook platforms also support detection and blocking of the IOCs listed below:
| Indicator | Notes |
|---|---|
sfrclak.com |
C2 domain; RAT callback and payload delivery |
callnrwise.com |
Associated attacker infrastructure |
142.11.196.73 |
Suspected attacker-controlled asset |
142.11.199.73 |
Suspected attacker-controlled asset |
plain-crypto-js@4.2.1 |
Malicious npm package (postinstall loader) |
axios@1.14.1 |
Backdoored Axios release |
axios@0.30.4 |
Backdoored Axios release |
The IPs listed above were identified through ThreatBook Research Team's pivot analysis as "highly likely" attacker-controlled assets. Organizations may wish to proactively block these at their discretion.
1 min read
Last week, ThreatBook's endpoint detection product, OneSEC EDR, identified and fully captured an active attack targeting OpenClaw users. The attack...
1 min read
1 min read
Executive Summary For months, the cybersecurity community tracked what appeared to be a sophisticated cybercrime organization dubbed "SilverFox"....